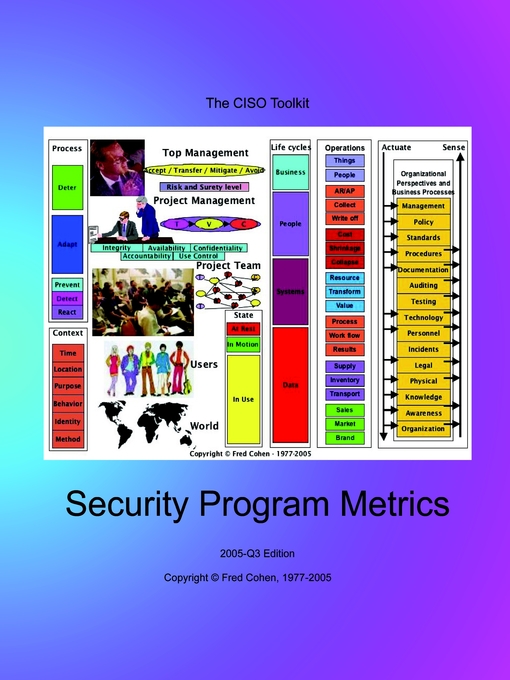
Security Metrics is the companion book to the Governance Guidebook. It includes:
-
Business modeling and how the business works in terms of the consequences of information technology failures.
-
Oversight including how laws, ownership, the board of directors, auditors, and the CEO impact the program, and how to turn business models into duties to protect.
-
Business risk management including turning duties to protect into what to protect and how well, threats, vulnerabilities, consequences, risk tolerance, interdependencies, risk aggregation, matching surety to risk,
-
Executive security management and governance at the organizational level including measuring management, policy, standards, procedures, documentation, auditing, protection testing, logical and physical security, personnel security practices, incident handling, disaster recovery, and business continuity planning, legal issues, knowledge and awareness levels and programs, and organizational structure and effectiveness.
-
Life cycle protection measures business, people, system., and data life cycles.
-
Contextual metrics cover time, location, purpose, behavior, identity, and methods.
-
Control architecture metrics measure security objectives including integrity, availability, confidentiality, use control, and accountability; and other aspects of control architecture like how access control approaches map clearances to classifications and control based on business utility, how functional units implement protective requirements, perimeter controls, access facilitation, and change management.
-
Protection process metrics cover work flow systems, how well you deter, prevent, detect, react, and adapt to attacks, protection of data in use, in transit, and in storage, and protective measures covers perception, structure, behavior, and content controls.
Together, these metrics provide comprehensive programmatic coverage of the issues that make a difference to the business, not just to a technologist.
Metrics are formed from repeatable measurements that are comparable. For example distance metrics, like yards or meters, can be measured by anyone who has access to the standard and any two things that are measured can be compared to determine which is shorter or longer. Security metrics that are useful should meet the same criteria. They should be repeatable and comparable.
Not all metrics are useful for all purposes. For example, it's very hard to relate the number of spyware elements scanned for by a spyware detector to the reduction in risk to the enterprise that uses it. In order for security metrics to be useful to the organization, they have to relate to organizational goals in terms of the organization's duty to protect. It may be easy to measure how many vulnerabilities are detected by a vulnerability scanner in a given month, but a reduction by two in the number of vulnerabilities may have almost no effect on reducing risk.
A presentation from the Computer Security Institute on what makes good and bad metrics is included here for your viewing interest. Buy it!