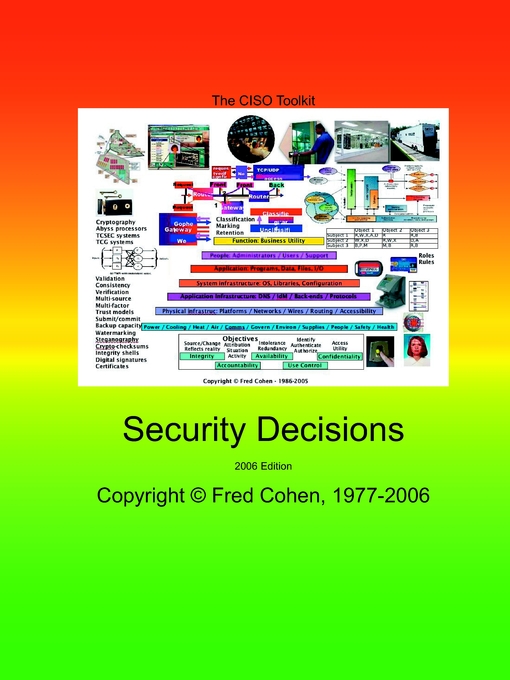
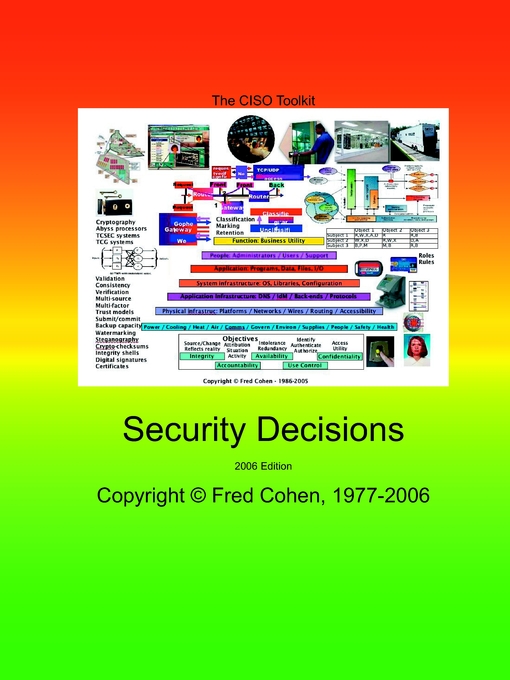
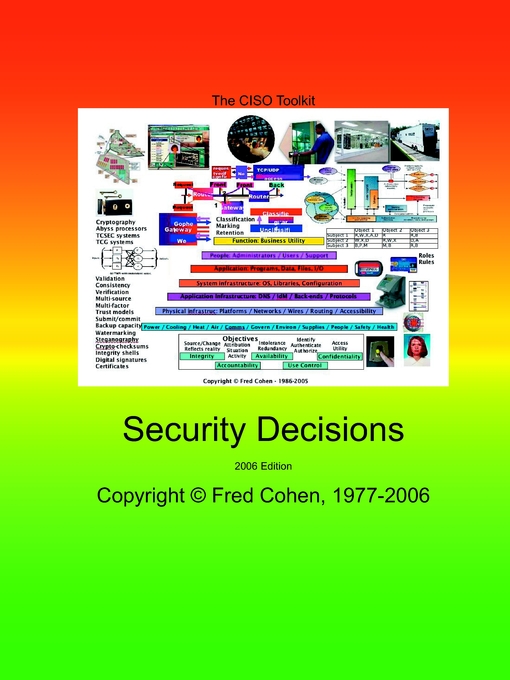
Security Decisions - 2006 Edition
Security Decisions provides a series of straight forward two-page decisions
about critical security issues. It is designed to provide clear linkage to the Governance
Guidebook with coordination between the governance issues identified and the decisions made.
This decisions book is organized as a series of relevant decisions that CISOs are making today
where each decision has different outcomes for different situations and environments.. The goal
is to provide a set of usable decisions that are codified in terms of the options, the decisions,
and the reasons behind those decisions so that if your reasons are different, you can make
similar decisions with your spin on them. Here are the decisions: Buy it!
Improving security: What's a good first step?
Defining risk: How should I define risk levels?
Spam: How should I handle it?
Spyware: How should I handle it?
Wireless: How should I handle network access?
Firewalls: What kind should I use?
Concealed networks: When should I use them?
Background checks: When should I do them?
Switches or hubs: Which should I use?
Penetration testing: What is it good for?
Open or closed source: Which is better for me?
Security awareness: What should my plan be?
Disaster recovery: How should I do planning?
Passwords: How often should we change them?
Remote access: How do I safely allow it?
Threats: How do I respond to computer extortion?
Encryption: When should I transmit encrypted?
Encryption: What should I store encrypted?
Incident detection: How should I detect attacks?
Incident response: Who you gonna call?
Security costs: How much should it cost?
Threats: Who would really try to attack me?
Backups: What should I back up and how often?
Backup retention: How long should I keep them?
Backups: How and where should I store them?
Security consultants: When should I use one?
Security policy: How much do I need?
Network zones: How should I zone my network?
Network zones: What should I put where?
Data center redundancy: How many do I need?
Backup facility distance: How far should I go?
Detection and response: How fast should I be?
Risk aggregation: How do I control it?
Change management: How should I handle it?
Security standards: Which ones should I use?
Your decisions
Summary and your questions
Upcoming Decisions
The Market Space
Your notes